Supabase Postgres Best Practices
Comprehensive guide for optimizing Postgres database performance and security using Supabase best practices
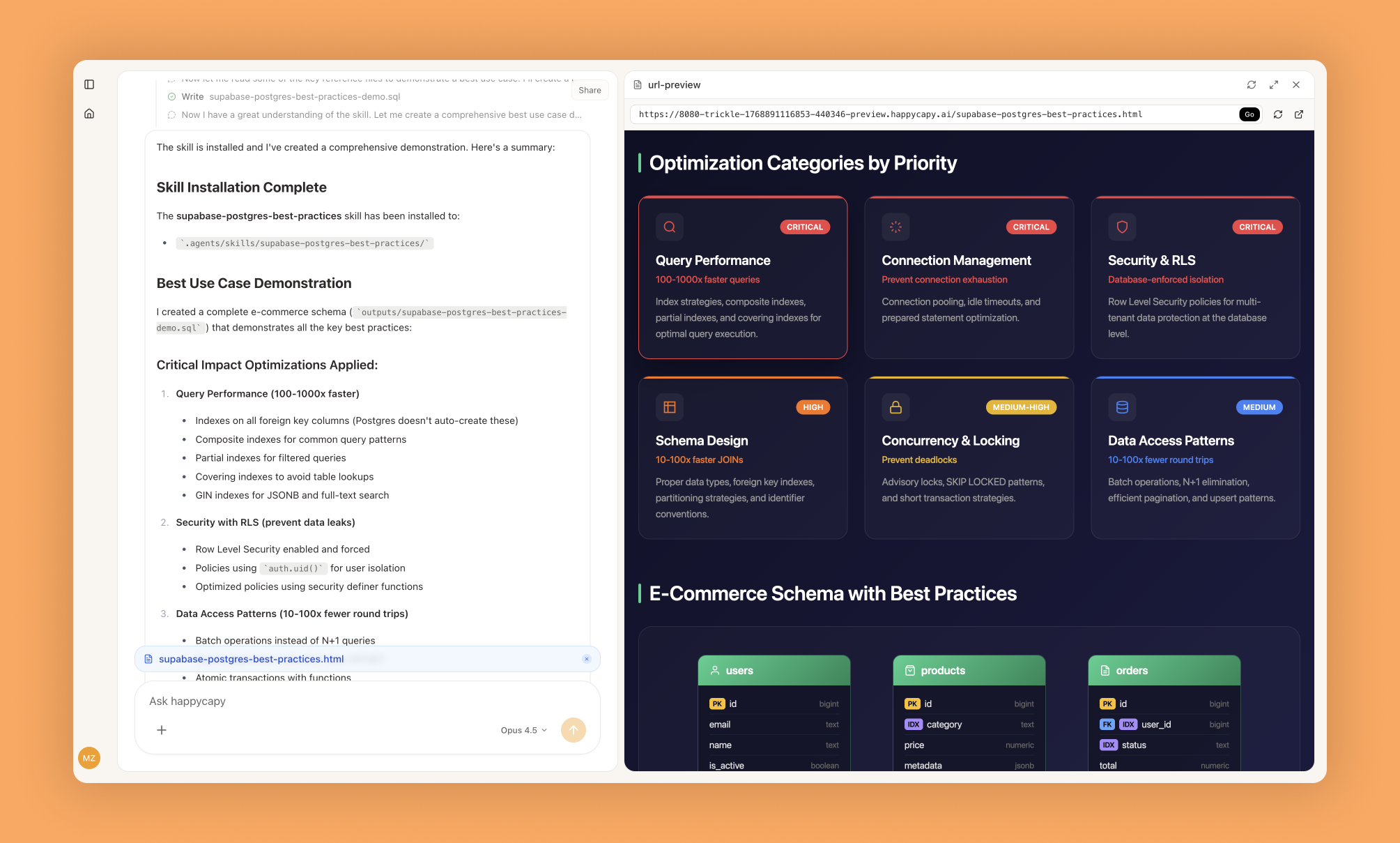
Database performance issues often stem from missing indexes, inefficient queries, or poor schema design. This comprehensive optimization guide from Supabase provides prioritized rules across query performance, connection management, security, and schema design to help developers write efficient Postgres code and avoid common pitfalls.
What Is This?
Overview
Supabase Postgres Best Practices is a structured performance optimization guide covering eight categories of Postgres rules, prioritized by impact from critical to incremental. Each rule includes detailed explanations, incorrect versus correct SQL examples, query plan analysis, and performance metrics.
This skill helps developers write optimized SQL queries, design efficient schemas, implement proper indexes, configure connection pooling, and leverage Postgres features correctly. The guide focuses on real-world optimization scenarios with actionable examples.
Rules are organized by impact level, letting developers focus on critical issues (query performance, connection management) before incremental optimizations. Each rule includes Supabase-specific notes when applicable.
Who Should Use This
Backend developers writing SQL queries or designing database schemas. Database administrators optimizing Postgres performance. Teams experiencing slow query performance or connection issues. Developers implementing Row-Level Security in Supabase. Anyone working with Postgres following industry best practices.
Why Use It?
Problems It Solves
Query performance degradation happens when developers miss indexing opportunities or write inefficient SQL. The guide provides concrete examples showing incorrect queries and their optimized versions with measurable improvements.
Connection pool exhaustion causes application failures under load. Best practices for connection management prevent these issues through proper configuration.
Schema design mistakes create performance bottlenecks difficult to fix later. Early application of schema design rules prevents problems during development.
Security vulnerabilities arise from improper Row-Level Security implementation. The guide covers RLS best practices specific to Supabase.
Core Highlights
Eight prioritized categories from critical to incremental impact. Concrete SQL examples showing incorrect and correct approaches. Query plan analysis with EXPLAIN output. Supabase-specific implementation notes. Coverage of indexes, connection pooling, RLS, concurrency, and monitoring.
How to Use It?
Basic Usage
Reference the guide when writing queries, designing schemas, or reviewing database performance. Rules are prefixed by category for quick identification.
Query performance: query-missing-indexes, query-full-table-scans
Connection: conn-pooling, conn-timeouts
Security: security-rls-performance
Schema: schema-partial-indexesSpecific Scenarios
For slow queries:
Check query-missing-indexes rule
Review EXPLAIN output for full table scans
Add appropriate indexes following examplesFor connection issues:
Review conn-pooling configuration
Implement connection limits per recommendations
Configure timeout settings appropriatelyFor RLS implementation:
Follow security-rls-performance guidelines
Review correct RLS policy examples
Optimize policies avoiding performance penaltiesReal-World Examples
An application experiences slow page loads querying user data. Developers discover their query lacks an index on the WHERE clause column. Following the query-missing-indexes rule, they add a B-tree index, reducing query time from 2 seconds to 50 milliseconds.
A service crashes during traffic spikes with connection pool exhaustion. The team discovers they have no connection pooling configured. Implementing Supavisor connection pooling following the conn-pooling rule eliminates crashes.
A team implementing multi-tenant Row-Level Security notices query performance degrading. They reference the security-rls-performance rule showing how to optimize RLS policies with proper indexes on tenant identifier columns, restoring normal performance.
Advanced Tips
Start with critical priority rules (query, connection, security) before optimizing lower-impact areas. Use EXPLAIN ANALYZE to verify improvements after applying recommendations. Review rule reference files for detailed SQL examples. Implement monitoring to catch issues early.
When to Use It?
Use Cases
Initial database schema design. Code review for SQL query performance issues. Performance tuning for slow database operations. Implementing secure multi-tenant applications with RLS. Scaling applications with connection pool issues. Learning Postgres optimization best practices. Training teams on database development standards.
Related Topics
Postgres query optimization and EXPLAIN plans. Database indexing strategies (B-tree, GiST, GIN). Connection pooling with PgBouncer and Supavisor. Row-Level Security implementation patterns. Schema normalization tradeoffs. Postgres monitoring and diagnostics tools. Supabase platform features.
Important Notes
Requirements
Basic understanding of SQL and relational databases. Access to Postgres database for testing. Ability to run EXPLAIN ANALYZE on queries. Familiarity with application query patterns. Understanding of database workload characteristics.
Usage Recommendations
Apply rules during development rather than after performance issues occur. Use EXPLAIN ANALYZE to verify optimization impact. Prioritize critical category rules before incremental optimizations. Test schema changes in non-production environments. Document which rules were applied. Regularly review rules as your application scales.
Limitations
Rules are general best practices requiring adjustment for specific workloads. Performance improvements vary based on data size and complexity. Some optimizations have tradeoffs requiring evaluation. Supabase-specific notes may not apply to self-hosted Postgres. Complex queries may require custom analysis.
More Skills You Might Like
Explore similar skills to enhance your workflow
Canvas Design
Design stunning visual artwork and professional graphic layouts using advanced digital canvas tools
Frontend Slides
Create stunning, animation-rich interactive HTML slide presentations
Brand Guidelines
Create comprehensive brand guidelines and style guides
Video Frames
Efficiently extract high-resolution individual frames from video files using powerful ffmpeg command-line tools
Infographic Creator
Design stunning data visualizations and infographics
Reddit Post Writer
Generate authentic Reddit posts through emotional truth